Credits: pinterest.com
Somewhere in the endless corridors of the internet, packets move like commuters in a megacity that never sleeps. Billions of requests cross the digital skyline every second—some legitimate, some curious, and some very much unwelcome. In the early days of the web, security teams believed they could control this chaos with a single wall: the firewall.
But walls belong to the past.
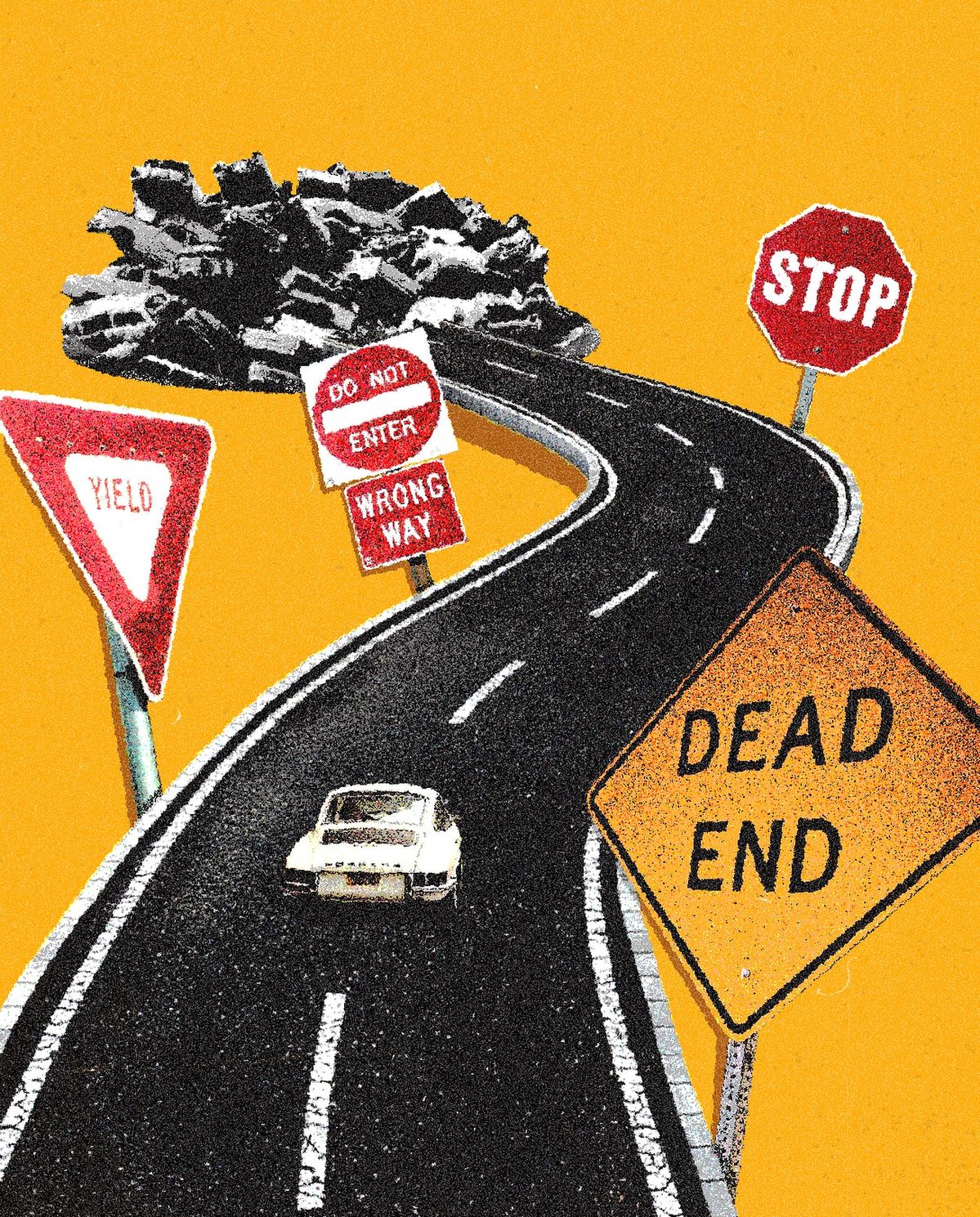
Modern infrastructure behaves less like a fortress and more like a shape-shifting city. Containers appear and disappear. Microservices multiply overnight. Entire environments spin up across continents and dissolve again before sunrise. In this reality, defending a fixed perimeter is like trying to guard a door in a building that keeps rebuilding itself.
This is where the idea of the elastic firewall emerges.
An elastic firewall is not a single device sitting quietly at the edge of the network. It is a distributed layer of intelligence that moves with the infrastructure it protects. As applications scale, security policies scale with them. As services migrate across environments, protections migrate too.
In a dystopian cyberpunk analogy, the elastic firewall is the surveillance grid of the digital metropolis—watching every lane of traffic, identifying patterns, and quietly reshaping the defenses when something looks wrong.
When a new service appears, rules apply instantly.
When traffic surges, inspection capacity expands.
When anomalies appear, automated responses can isolate suspicious activity before it spreads across the network.
The system bends without breaking.
This adaptability is critical because the threats themselves have evolved. Attackers no longer rely on slow manual probing. They deploy automated scanning systems, distributed bots, and AI-assisted reconnaissance. Static defenses struggle to keep up with this speed.
Elastic infrastructure, however, was built for motion.
Security teams increasingly design protection directly into deployment workflows. Firewall rules are no longer configured once and forgotten; they are defined as code, versioned alongside the infrastructure, and deployed automatically as environments change.
This integration aligns naturally with modern engineering practices such as <a href=”https://www.devopsteam.io/”>devops</a>, where development, operations, and security collaborate inside the same automated pipelines.
The result is a system that feels almost alive.
Instead of waiting for administrators to notice a breach attempt hours later, elastic defenses respond immediately. Instead of patching vulnerabilities after deployment, teams design security into the architecture from the beginning.
In the neon-lit dystopia of the modern internet, the network never stops evolving. Neither do the threats that inhabit it.
But somewhere inside the cloud, quietly stretching and adapting, the elastic firewall continues its silent work—filtering ghost traffic, reshaping its defenses, and keeping the digital city standing one packet at a time.